Leading secure ATM solution
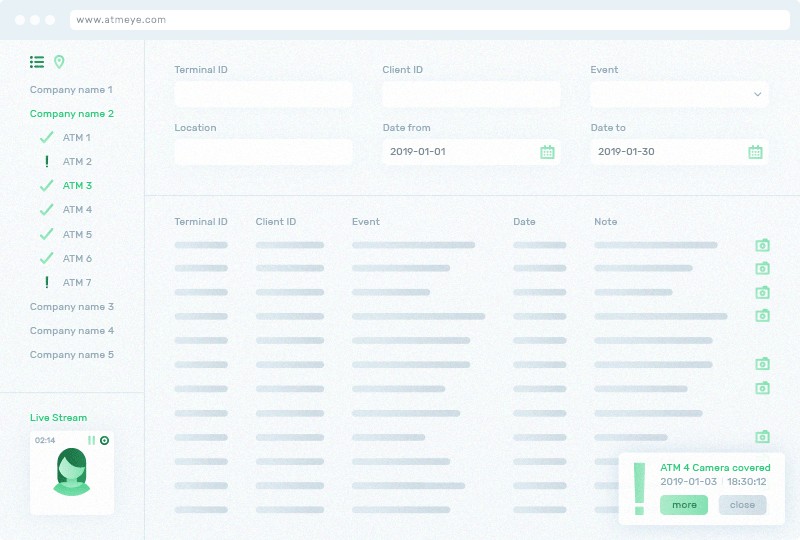
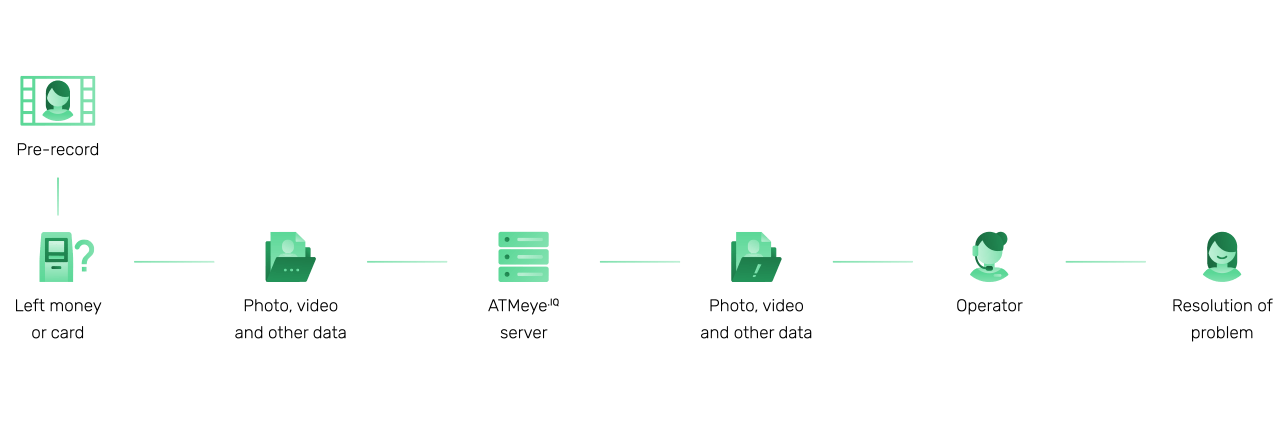
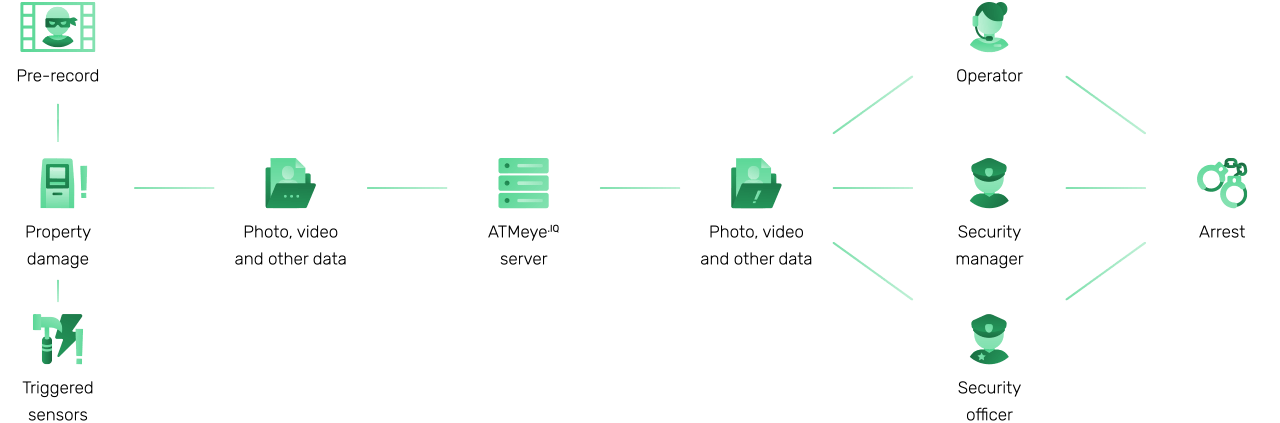
ATMeye.iQ is an ATM software designed to ease the work of ATM security services. Easily secure your ATM network with real time video analysis, anti skimming devices, facial recognition and various sensors.
Read more in ATM Security risks in Asia-Pacific region.