All You Need to Know About ATM Skimming Devices
2022-06-27What is ATM skimming
Skimming is a type of fraud that occurs when an ATM is hacked by a skimmer. In the security field, a skimmer means any hardware device for stealing information stored on payment cards. Skimmers consist of a card reader with a chip, a small camera or a fake keypad for entering the PIN-code.
Important: To protect against skimming, first of all avoid ATMs located in places with poor lighting. Before inserting the card, you should move or pull the card reader and keypad to make sure that these elements do not move. Pay attention to the protruding components that do not coincide with the rest of the ATM (unevenly glued stickers, extra holes, etc.). It is better to cover the keypad with your hand while entering the PIN-code. It is also important to monitor accounts for improper transactions.
Types of skimmers:
✔ Software skimmers – these skimmers target software components of payment systems and platforms (such as the operating system).
✔ Web skimmers – in this case, attackers often use malicious JavaScript code.
Skimmers help fraudsters steal bank card data (details, PIN code and other information recorded on the magnetic strip). Portable skimmers allow to make a copy of the card when it ends up in the hands of fraudsters.
Skimmers are attached to ATMs using the usual double-sided adhesive tape or a special fastener. Pay attention to the keypad for entering the PIN-code and the slot for card insertion before using an ATM. A skimming device can change the shape of the keypad or keys. For example, if the keypad was concave, the overlay will make the panel flatter. The keys may be too recessed in the keyboard panel or protruding.
What does an ATM skimmer look like
Fraudsters can try to theft the data of a bank card of its owner, using special copying devices in the points of use of cards (ATMs, payment terminals, etc.). After that the criminals make a card with the data of its owner and withdraw money. There are several skimming techniques, we will describe some of them.
ATM overlay
Overlays are devices placed over the keypad and used to recognize the PIN code when entered by the bank card owner. To prevent such crimes banks install surveillance cameras.
Fraudsters install a fake keypad on top of the original keypad on an ATM. As a result, the counterfeit keyboard remembers the keys being typed and transmits the keystrokes to the real keys. The ATM responds as usual, so the switch is difficult to detect. The criminals then take the overlay, decipher the recording, and learn the cardholder’s PIN number. Using the stolen data, the criminals can make a copy of the card.

Bluetooth skimmer
These almost invisible devices receive bank card information and send it to a nearby device via Bluetooth technology.
Bluetooth skimmers can be installed right in front of store or gas station employees. One perpetrator can then pretend to pump gasoline while the other distracts the cashier. As a result, the skimmer will silently and inconspicuously collect the PIN-code and card data of its owner.
Black box hack
This hacking is done with special devices called black boxes. They are specifically programmed single-board microcomputers.
After gaining access to the inside of the ATM, the criminal opens the casing and connects a device that forces the ATM to dispense all the cash. Quite often, black boxes are controlled from a common smartphone.

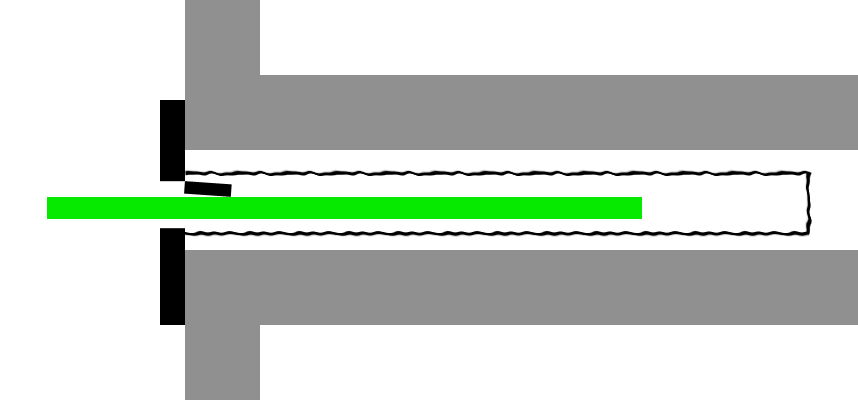
Card skimmer
A credit card skimmer is a device designed to steal information by reading the magnetic tape. After collecting the information, such skimmers are used to create a clone of the card and use it for fraudulent purposes.
These skimmers are attached to the ATM card acceptor and collect information from each card that enters it. To guard against such activities, users should carefully inspect the card slot for hinged panels and other atypical components.

Hidden camera
Hidden cameras are attached to the ATM or are located near it (there are cases when cameras are mounted in the stands for the bank’s promotional brochures). Miniature cameras are directed to the ATM keyboard and are designed to record PIN-codes entered by cardholders.
The presence of the camera can be evidenced by a small depression resembling a black dot. Before using the ATM, you should carefully inspect it for the slightest holes and recesses. In addition, you should cover the keypad with your free hand when entering the PIN-code.
Malware
Malware attack allows fraudsters to force ATMs to dispense cash without reflecting withdrawals on any bank accounts. Malware includes Ploutus, Cutlet Maker and other programs.
The malware is installed via a USB flash drive which contains the virus. This type of attack resembles the black box, but in this case the criminals do not even need to install any equipment inside the machine.
What happens if a credit card is skimmed
Any user of a credit or debit card who uses it in a store, restaurant or gas station can suffer from skimming. Fraudsters can use stolen card information in a variety of ways. For example, an attacker may sell stolen data or make a fake credit card to make fraudulent online purchases.
Fraudulent credit card payments are easier to dispute than payments made through a debit card. Most credit cards have a zero liability policy, meaning that the cardholder is not responsible for paying back the funds to the issuer when fraudulent activity occurs.
Important: To protect against skimming you should regularly monitor your credit card activity and check your bank statements in detail. Suspicious activity should be reported as soon as possible to the bank that issued the particular card.
Some cards have a special alert that notifies the cardholder possible fraudulent charges. After that, the user is usually given a new bank card with a new number.
How to spot ATM skimming devices
There are different methods to spot skimming devices for ATMs.
It is difficult for a non-professional to notice a bank card reader. For many bank customers the skimmer will not cause any suspicions. This device is attached to the body of the ATM, to the card acceptor.
The skimming device consists of three elements:
✔ the reading magnetic head – is responsible for reading the data from the magnetic strip;
✔ converter – a miniature fraud device, which converts the read information into a digital code;
✔ storage device – designed to write the digital code to the data carrier.
Skimmers can work on the principle of accumulating information about users or transmitting data about cards to fraudsters via a radio channel to the receiving device.
Below you will find a step-by-step algorithm for detecting a skimming device.
Step 1: Examine the card reader for signs of tampering
Carefully inspect the machine’s card reader. It should be firmly attached to the ATM. Be cautious if tape or plastic fragments are sticking out from under the card reader. Also, there should be no traces of glue around the card reader.
Step 2: Look around for a hidden camera
The cameras installed by the bank are quite visible. Look around the machine for a small hidden camera installed by fraudsters. As we mentioned earlier, fraudsters attach such devices to ATMs in order to find out the cardholder’s PIN code. Most often the cameras are located above the screen or at the counters. A mug or a book can hide the camera.
Step 3: Check the top of the ATM for unusual plastic pieces
There should be no suspicious plastic parts on top of the machine. Often, such elements are made in a rectangular shape and attached with tape. Inside the rectangular plastic there may be a device for reading the card information. If you see a suspicious part, you should try to move it. The movability may indicate the presence of a skimmer.

Step 4: Examine the key pad for larger keys or unusual thickness
Before using the ATM, you should inspect the keypad. Too large buttons or keys of unusual thickness may cause suspicion. The keypad may be suspiciously new or slightly protruding over the case. Factory-inspired keypads fit as snugly as possible. Fraudsters may install a fake keypad over the real one to find out the PIN code.
Step 5: Check to see if lines, arrows, and other graphics are covered up
Hidden graphic elements may indicate the presence of fake ATM components. A standard machine should be devoid of hidden lines and arrows. There may be a skimmer under the hidden card readers, so the graphic elements and the card reader should be at a distance from each other.
Step 6: Wiggle the card scanner to see if it moves or budges
The card reader should be moved before inserting the card. Modern ATMs are characterized by a robust and reliable construction, so a moving card reader can indicate the presence of a skimmer. The skimmer can be attached by means of tape or glue.
Step 7: Press down on the key pad to see if it feels sticky or spongy
There should be no unnecessary keys on the ATM keyboard. Check to see if the keypad is sticky, deformed, or stiff. These characteristics may indicate the presence of a fake overlay.
How to avoid card skimming
Banks are struggling with fraud in every way possible, but the perpetrators regularly come up with new ways to commit fraud. There are several measures to help users not to become a victim of skimming.
Here are some useful tips to help avoid skimming.
Use an ATM that is inside a bank as much as possible
ATMs that are inside branches are better guarded and thoroughly checked by bank employees. There are a large number of machines in branches, and it would be difficult for fraudsters to install a skimmer on each one.
Use ATMs in a well-lit location
If the machine is standing in a dim room, it is better not to use it. To withdraw cash, use well-lit ATMs that are in crowded places.
Use mobile wallets
Such virtual wallets store all necessary payment card information on your mobile device. Mobile wallets allow to make secure payments on the Internet without the risk of fraudsters using card data.
Download skimmer detecting apps
A special application will help to find out if there is a bank card skimmer nearby. This application scans Bluetooth signals and searches for suspicious connections.
Report any problems
If something seems suspicious, inform the administration of the place where the ATM is installed. Often vigilance can help prevent a crime.
Use ATMs with jitters
A jitter is an overlay on a card reader that causes it to vibrate when you enter it. The vibration will prevent fraudsters from copying the magnetic strip on the card, so attackers don’t install skimmers on such devices.
Beware of the Lebanese loop
This scam, common among tourists, involves installing a blocker inside the card reader. When a user attempts to withdraw money, the card may “get stuck.” Under no circumstances should you enter a PIN. The correct solution is to call the hotline of the bank that issued the particular card.
Anti-skimming systems
Versatile protection against skimming and other criminal activities is provided by BS/2’s advanced ATM video surveillance software, ATMeye.iQ. ATMeye.iQ is a comprehensive solution that simplifies the work of security and support services. The software is equipped with special sensors, makes it possible to detect readers installed by fraudsters, and block terminal operation.
A separate anti-skimming solution, ASM.ATMeye.iQ, helps prevent attacks on ATMs at every stage. With this solution, any attempt to install skimming equipment or close the video surveillance camera will activate protection scenarios. In this case, security specialists will be sent a real-time notification with information about the incident, a photo of the suspect and video of the scene.
Conclusion
To summarize, we should note that skimming devices are devices that allow reading information from cards during a transaction. To steal card data, attackers need to copy the magnetic stripe on the card and the PIN-code.
ATM owners should take a proactive approach to protect customers from fraud. Banks should use modern software to protect against skimming. The main advantages of such solutions are easy management of the fleet of devices, simplification of security service work, access to photo and video from the scene, and the ability to view video and photos in real time.
FAQ
Any owner of a bank card with a magnetic stripe can become a victim of skimming. The information obtained by criminals allows them to produce a duplicate and pay in online stores or completely empty the bank account. Fraudsters can install portable magnetic stripe readers in hotels, cafes, restaurants and stores. Banks and cardholders need to take care of card protection.
Below you will find answers to several questions about ATM skimming devices.
Can chip cards be skimmed?
Yes. Chip cards are skimmed because of their magnetic stripe. Attackers often target ATMs and gas stations.
What if I find a skimmer on an ATM?
If you find a skimmer, you should contact bank employees. If you notice suspicious activity near an ATM when the bank branch is closed, it is best to report it to the police.
How prevalent is ATM skimming?
The use of special devices, which are attached directly to the ATM as well as to any receiving slot of the card acceptor, is a fairly common type of fraud. In recent years, there has been an increase in cases of skimming and other criminal activities with bank cards. In January 2021, a major skimming scam was uncovered in New Jersey.
What's the difference between skimming and shimming?
Shimming is a type of skimming. The main difference between shimming and skimming is the inability to detect shimmers with the naked eye, because instead of bulky pads, shimming uses a compact, flexible device with a thickness of only 0.1-0.2 mm.
How can ATM skimming be prevented?
To protect against skimming, it is best to use ATMs that are under video surveillance. You should not use your bank card in suspicious places. In addition, it is better to switch on SMS-informing about operations with a bank card. PIN-code should be typed quickly and with both hands.
Can Apple or Google Pay be skimmed?
Apple Pay and Google Pay do not require credit card information, so users are protected from data interception. Apple Pay and Google Pay use one-time payment tokens to authorize payments, so retailers don't get credit card information online.


